Watchlists & Sanctions: Business Search
Watchlist Screening in Business Search
Sanctions and watchlist screening is a critical compliance requirement for financial institutions, fintech companies, and businesses handling payments or extending credit. This guide explains how Baselayer performs watchlist checks as part of every Business Search, where to find results in the API response, and how to interpret them for your compliance workflows.
For a deeper understanding of sanctions compliance concepts, see the Watchlists, Sanctions & Compliance Screening guide. For standalone sanctions and PEP checks outside of Business Search, see the Watchlists & Sanctions: Standalone Checks guide.
How Watchlist Screening Works in Business Search
Baselayer automatically performs watchlist screening as part of every Business Search. No additional configuration is required — screening runs by default when you submit a search.
What Gets Checked
When you submit a Business Search, Baselayer runs watchlist checks on:
- Business name submitted in the search request
- Alternative business names submitted via the
alternative_namesfield (if provided) - Officer names submitted via the
officer_namesfield (if provided) - Business legal name found in the Baselayer business profile (from Secretary of State records)
- Alternative business names found in the Baselayer business profile (from Secretary of State records)
- All officers identified in the Baselayer business profile (from SoS records and other sources)
This means even if you don't provide officer names or alternative business names in your search input, Baselayer will still screen any names and officers it identifies in the business profile against all applicable watchlists.
Watchlists Scanned
Every Business Search screens against the following official government watchlists:
| List | Abbreviation | Administering Agency |
|---|---|---|
| Specially Designated Nationals | SDN | OFAC (Treasury) |
| Sectoral Sanctions Identifications List | SSI | OFAC (Treasury) |
| Capta List | CAP | OFAC (Treasury) |
| Foreign Sanctions Evaders | FSE | OFAC (Treasury) |
| Non-SDN Menu-Based Sanctions | NS-MBS | OFAC (Treasury) |
| Non-SDN Iranian Sanctions Act | NS-ISA | OFAC (Treasury) |
| Non-SDN Chinese Military-Industrial Complex Companies | NS-CMIC | OFAC (Treasury) |
| Non-SDN Palestinian Legislative Council | PLC | OFAC (Treasury) |
| Entity List | EL | Bureau of Industry and Security |
| Denied Persons List | DPL | Bureau of Industry and Security |
| Military End User List | MEU | Bureau of Industry and Security |
| Unverified List | UVL | Bureau of Industry and Security |
| ITAR Debarred | DTC | State Department |
| Nonproliferation Sanctions | ISN | State Department |
| Politically Exposed Persons** | PEP | Multiple sources |
| FBI Most Wanted / Criminal Lists | FB | FBI |
| HHS OIG List of Excluded Individuals/Entities | LEIE | HHS Office of Inspector General |
| IRS Exempt Organizations | IEO | Internal Revenue Service |
| Consolidated Canadian Autonomous Sanctions List | CNS | Government of Canada |
For a detailed explanation of each list and its compliance implications, see the Watchlists, Sanctions & Compliance Screening guide.
Baselayer summarizes the above individual lists in the below umbrella categories (OFAC, CSL, etc.):
| Code | Full Name | Status |
|---|---|---|
| OFAC | Dept. of Treasury, Office of Foreign Assets Control | Always runs automatically |
| CSL | Dept. of Commerce, Consolidated Screening List | Always runs automatically |
| CNS | Consolidated Canadian Autonomous Sanctions List | Always runs automatically |
| FBI | FBI Wanted List | Always runs automatically |
| OIG | HHS OIG List of Excluded Individuals/Entities (LEIE) | Always runs automatically |
| IEO | IRS Exempt Organizations List | Runs when TIN is provided |
| PEP | Politically Exposed Persons | Runs when Order.Pep option is included |
Automatic Checks
Five watchlists run automatically with every Business Search: OFAC, CSL, CNS, FBI, and OIG. No additional configuration or input is required.
Conditional Checks
Two watchlist checks require specific conditions:
IEO (IRS Exempt Organizations) — Only runs when a tin is provided in the search request. If you need IEO screening, include the business's TIN in your search.
PEP (Politically Exposed Persons) — Only runs when Order.Pep is included in the search options:
{
"name": "Acme Corporation",
"address": "123 Main St, New York, NY 10001",
"options": ["Order.Pep"]
}Without this option, PEP checks will not be performed. If you are onboarding high-value customers or operating in regulated industries (banking, crypto, lending), consider always including Order.Pep in your search options.
Understanding the Response
When Baselayer returns a Business Search response, watchlist results appear in two separate locations. Understanding this structure is essential for correctly identifying all potential matches.
1. Top-Level watchlist_hits (Search-Level)
watchlist_hits (Search-Level)The top-level watchlist_hits array contains matches for the data you submitted in your search request: the business name, alternative names, and officer names you provided.
{
"id": "search-id-123",
"name": "11420 CORP.",
"address": "5599 NW 23rd Ave, Boca Raton, FL 33496",
"tin": "270746046",
"watchlist_hits": [
{
"code": "OFAC",
"name": "Department of Treasury, Office of Foreign Assets Control",
"count": 2,
"details": [...]
}
],
"business": {...}
}2. Business-Level watchlist_hits (Profile-Level)
watchlist_hits (Profile-Level)The watchlist_hits array nested inside the business object contains matches for data found in Baselayer's business profile: the business's legal name, alternative names from Secretary of State records, and officers identified from SoS records and other sources.
{
"business": {
"id": "business-id-456",
"name": "11420 CORP.",
"watchlist_hits": [
{
"code": "CSL",
"name": "Department of Commerce, Consolidated Screening List",
"count": 1,
"details": [...]
}
]
}
}Why Two Locations?
The two-location structure helps you distinguish between:
- What you submitted (search-level): useful for understanding if the applicant's provided information matches a watchlist
- What we found (business-level): useful for understanding if the verified business entity itself has sanctions exposure based on official records
In practice, you should check both locations for any positive matches. If either location shows a count > 0, that's a compliance flag.
Important: No Split Between Business Names and Officers
Within each watchlist_hits array, matches are not separated by type. Business names, alternative names, and officer names all appear together in the same list. For example, if the business name matches OFAC and one of its officers also matches OFAC, you'll see both in the same details array with a count of 2.
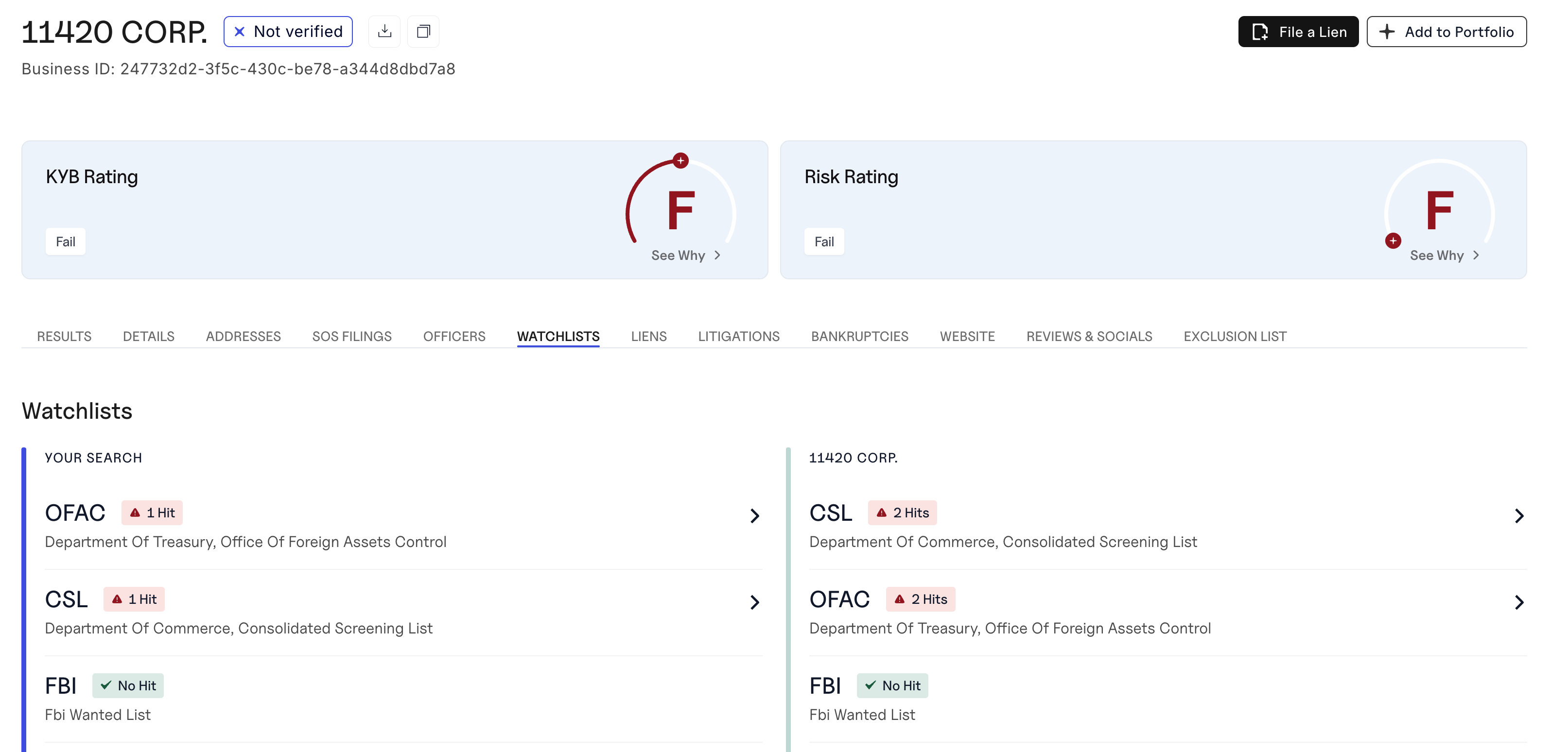
Visual Representation in the Console
In the Baselayer Console, watchlist results are displayed side-by-side:
- Left panel: "Your Search" — shows matches for the data you submitted
- Right panel: "Business Name" — shows matches for the Baselayer business profile
This mirrors the two-location structure in the API response.
Reading Watchlist Results
Structure of a Watchlist Hit
Each entry in the watchlist_hits array follows this structure:
{
"code": "OFAC",
"name": "Department of Treasury, Office of Foreign Assets Control",
"count": 2,
"details": [
{
"source": "SDN",
"entity_number": "24430",
"type": "Entity",
"programs": "VENEZUELA",
"name": "11420 CORP.",
"title": null,
"addresses": [
"5599 NW 23rd Avenue, Boca Raton, FL, 33496, US"
],
"alt_names": [],
"source_list_url": "https://sanctionslist.ofac.treas.gov/Home/SdnList"
},
{
"source": "SDN",
"entity_number": "24427",
"type": "Individual",
"programs": "VENEZUELA",
"name": "SARRIA DIAZ, Rafael Alfredo",
"title": null,
"addresses": [...],
"alt_names": ["SARRIA-DIAZ, Rafael A", "SARRIA, Rafael"],
"source_list_url": "https://sanctionslist.ofac.treas.gov/Home/SdnList"
}
]
}Key Fields
code: The watchlist identifier (OFAC, PEP, CSL, etc.)name: Human-readable name of the watchlistcount: Number of matches found (0 means no matches)details: Array of individual matches, including names, addresses, and sanctions program information
Identifying Matches
Any watchlist entry where count > 0 indicates a positive match requiring review. Even if only one name matches, this is a compliance flag that must be investigated.
The Similarity Threshold
Baselayer uses fuzzy name matching to identify potential watchlist matches. Because names can be spelled differently, abbreviated, or contain typos, exact string matching would miss many legitimate matches.
Default Thresholds
For Business Search requests, Baselayer uses the following default similarity thresholds to ensure comprehensive coverage:
| Watchlist | Default Similarity Threshold |
|---|---|
| OFAC, CSL, CNS, FBI, OIG, IEO | 0.7 (70%) |
| PEP (Politically Exposed Persons) | 0.8 (80%) |
These defaults are intentionally set lower than standalone check defaults (which use 0.9) to maximize coverage during business verification. A name must meet or exceed the threshold to be flagged as a potential match.
Custom Thresholds
Baselayer can configure custom similarity thresholds per customer account. It's common for customers to request stricter thresholds (to reduce false positives) or looser thresholds (to maximize coverage) depending on their risk appetite and regulatory requirements.
Custom threshold changes are applied upon written request and confirmed in writing by Baselayer.
Choosing the Right Threshold
The defaults of 0.7 and 0.8 work well for most organizations, providing comprehensive coverage while keeping false positives manageable. Consider adjusting based on your risk tolerance:
- Stricter thresholds (0.85–0.9+): Fewer false positives requiring manual review, but may miss legitimate matches with significant name variations
- Looser thresholds (0.6–0.7): Maximum coverage for high-risk use cases, but expect more false positives
Contact your Baselayer account representative to discuss threshold adjustments for your account.
Screening Configuration and Compliance Documentation
For auditors, examiners, and compliance teams, Baselayer can provide written confirmation of the screening configuration applied to your account. This documentation typically includes:
- Which watchlists are scanned — A full list of all watchlists included in every Business Search, along with their run conditions (automatic vs. conditional)
- Similarity thresholds — The configured match sensitivity for each watchlist
- What names are screened — Confirmation that business names, alternative names, and all identified officers are screened against all applicable watchlists
- Change control — Confirmation that settings are only modified upon explicit written request
This documentation is designed to satisfy auditor and examiner inquiries about your sanctions screening program. Contact your Baselayer account representative to request a screening configuration confirmation for your account.
Implementation: Checking for Watchlist Hits
def has_watchlist_hits(search_response):
"""
Check if there are any watchlist matches at either the search
or business level.
Returns: (bool, list of watchlist codes with hits)
"""
hits = []
# Check search-level watchlist hits
for watchlist in search_response.get('watchlist_hits', []):
if watchlist.get('count', 0) > 0:
hits.append(watchlist['code'])
# Check business-level watchlist hits
business = search_response.get('business', {})
for watchlist in business.get('watchlist_hits', []):
if watchlist.get('count', 0) > 0:
hits.append(watchlist['code'])
return len(hits) > 0, hits
# Usage
search_response = {} # Your Business Search response
has_hits, watchlist_codes = has_watchlist_hits(search_response)
if has_hits:
print(f"⚠️ Watchlist hits found: {', '.join(watchlist_codes)}")
# Trigger manual review or reject
else:
print("✅ No watchlist hits")Best Practices
Always check both response locations. Don't just check the top-level watchlist_hits — also check the business.watchlist_hits array. A match in either location is a compliance flag.
Treat any count > 0 as a flag. Even a single match requires investigation. Don't ignore low counts.
Review the details. Don't stop at the count — examine the details array to understand what matched, which sanctions program it's tied to, and the associated addresses and alternative names. This context helps you determine if it's a true match or a false positive.
Consider match type. Matches marked as "type": "Individual" are people, while "type": "Entity" are businesses. This distinction matters for your review process.
Use PEP checks for higher-risk scenarios. If you're onboarding high-value customers or operating in regulated industries, always include Order.Pep in your search options.
Handle false positives gracefully. Not every match is a true positive. Common false positives include common names, similar business names in different industries, and entities with the same name but different locations. Always investigate before rejecting.
Keep records. Log all watchlist screening results, including timestamp, input data, and match details. Regulators may require proof of screening.
Don't rely solely on automated screening. Watchlist screening is part of a broader compliance program. Combine it with manual review for positive matches, enhanced due diligence for high-risk matches, and ongoing monitoring via Portfolio Monitoring.
Next Steps
- Learn the fundamentals: Read Watchlists, Sanctions & Compliance Screening for compliance concepts
- Run standalone checks: See Standalone Sanctions & PEP Checks for independent screening outside of Business Search
- Explore Business Search: See the Business Search Guide for full API details
- Set up monitoring: Use Portfolio Monitoring to continuously screen your customer base
Updated 24 days ago
